Filter by
SubjectRequired
LanguageRequired
The language used throughout the course, in both instruction and assessments.
Learning ProductRequired
LevelRequired
DurationRequired
SkillsRequired
SubtitlesRequired
EducatorRequired
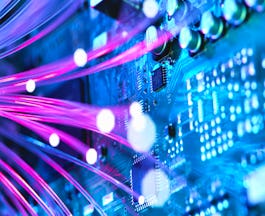
Results for "security best practices"
Skills you'll gain: Incident Response, Computer Security Incident Management, Intrusion Detection and Prevention, Threat Detection, Cyber Threat Hunting, Incident Management, Cybersecurity, Security Management, Security Information and Event Management (SIEM), Data Integrity

Skills you'll gain: Systems Administration, Cloud Infrastructure, IT Infrastructure, Lightweight Directory Access Protocols, Active Directory, Disaster Recovery, Server Administration, Linux Administration, Cloud Computing, Servers, Windows Servers, Network Infrastructure, Data Storage, Virtualization, User Accounts

Skills you'll gain: Data Ethics, Data Analysis, Analytics, Data-Driven Decision-Making, Google Sheets, Business Analytics, Spreadsheet Software, Analytical Skills, Data Sharing, Data Cleansing, Data Processing, Data Strategy, Data Visualization Software, SQL
 Status: [object Object]
Status: [object Object]Skills you'll gain: Istio, Node.JS, Software Development Life Cycle, Unit Testing, Cloud Computing Architecture, Server Side, Application Deployment, Kubernetes, React Redux, Cloud Services, Django (Web Framework), Object-Relational Mapping, OpenShift, Git (Version Control System), Full-Stack Web Development, HTML and CSS, Cloud Computing, Jupyter, Generative AI, Interviewing Skills

University of Minnesota
Skills you'll gain: Performance Management, Performance Appraisal, Performance Review, Employee Performance Management, Compensation Management, Compensation Strategy, Compensation and Benefits, Constructive Feedback, Workforce Planning, Human Resource Strategy, Human Resources, Employee Onboarding, Recruitment, Human Resources Management and Planning, Recruitment Strategies, Full Cycle Recruitment, Compensation Analysis, Talent Acquisition, People Management, Job Analysis

Skills you'll gain: Encryption, Identity and Access Management, Public Key Infrastructure, Endpoint Security, Cryptography, Network Security, Cybersecurity, Threat Detection, Cyber Attacks, Cryptographic Protocols, Data Security, Email Security, Computer Security Awareness Training, Advanced Encryption Standard (AES), Security Awareness, Key Management, Secure Coding, Technical Support and Services, Information Technology, Cyber Security Strategy
Skills you'll gain: Cloud Security, Google Cloud Platform, Identity and Access Management, OAuth, Kubernetes, Encryption, Cloud API, Application Security, Authorization (Computing), Data Encryption Standard, Cloud Storage, Authentications, Data Security, Application Programming Interface (API), Virtual Machines, Vulnerability Scanning, Key Management

Skills you'll gain: React Native, Android Studio, Restful API, Version Control, User Research, UI/UX Research, Usability Testing, Git (Version Control System), Data Structures, Jest (JavaScript Testing Framework), Unix Commands, Android Jetpack, Android Development, Persona (User Experience), GitHub, Interaction Design, Kotlin, User Experience Design, User Interface and User Experience (UI/UX) Design, Mobile Development

Skills you'll gain: Data Storytelling, Data Visualization, Data Presentation, Interactive Data Visualization, Tableau Software, Presentations, Data Visualization Software, Dashboard, Web Content Accessibility Guidelines, Design Elements And Principles

ISC2
Skills you'll gain: Network Security, Cybersecurity, Cyber Attacks, Infrastructure Security, Threat Detection, Computer Networking, Data Centers, General Networking, Network Planning And Design, Network Protocols, Network Model, Cloud Computing, TCP/IP

Erasmus University Rotterdam
Skills you'll gain: Microsoft Excel, Excel Formulas, Verification And Validation, Business Modeling, Technical Documentation, Data Validation, Asset Protection, Maintainability, Information Architecture, Data Integrity, Data Management

Cisco Learning and Certifications
Skills you'll gain: Cyber Threat Intelligence, Threat Detection, Workflow Management, Stakeholder Engagement, Cyber Operations, Cybersecurity, Stakeholder Management, Security Information and Event Management (SIEM), Incident Response, Security Management, Computer Security Incident Management, Cyber Attacks, Stakeholder Communications, Incident Management, Event Monitoring, Security Controls, Data Security, Customer Relationship Building, Network Security, Team Oriented
In summary, here are 10 of our most popular security best practices courses
- Incident Response and Digital Forensics: IBM
- System Administration and IT Infrastructure Services: Google
- Foundations: Data, Data, Everywhere: Google
- IBM Full Stack Software Developer: IBM
- Human Resource Management: HR for People Managers: University of Minnesota
- Cybersecurity Fundamentals: IBM
- Security Best Practices in Google Cloud - Español: Google Cloud
- Meta Android Developer: Meta
- Share Data Through the Art of Visualization: Google
- Network Security: ISC2










